DKIM signing in Office 365
By · · 2 mins read · Tech
This week I came across a post from Terry Zink (http://blogs.msdn.com/b/tzink/archive/2015/10/08/manually-hooking-up-dkim-signing-in-office-365.aspx) on how to activate DKIM signing for outbound email messages in Office 365.
I’ve been waiting for this feature for quite some time and was keen to get it going for both my personal email (on shaun.net) and my business email (on ewing.net.au).
To get started the first thing I needed to do was create two CNAMEs in the DNS zone for shaun.net. This provides two DKIM key selectors - which allows for automatic key rotations.
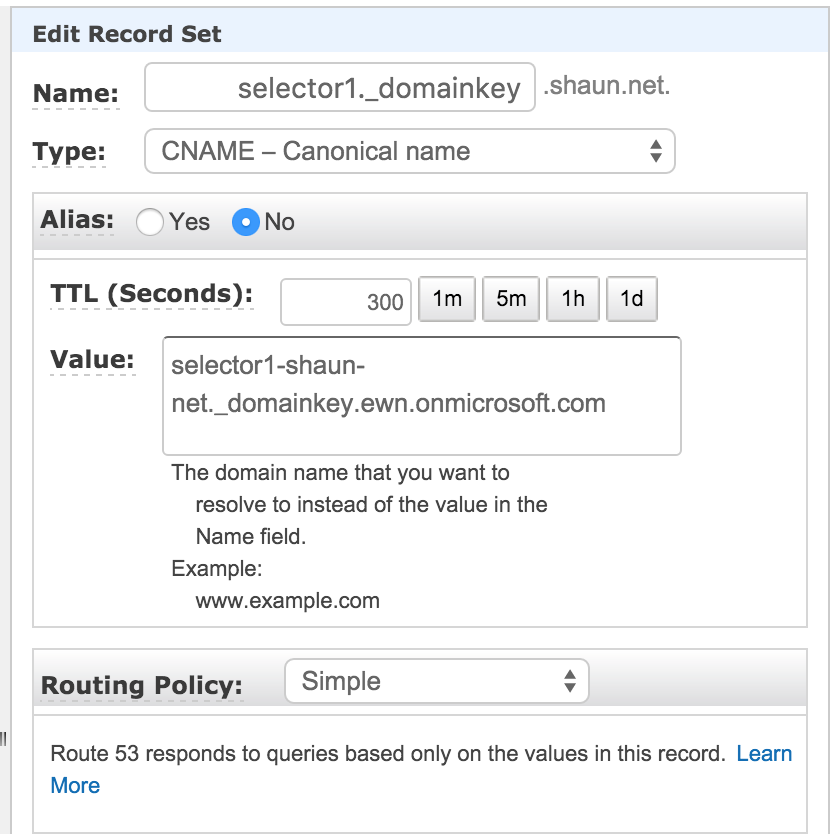
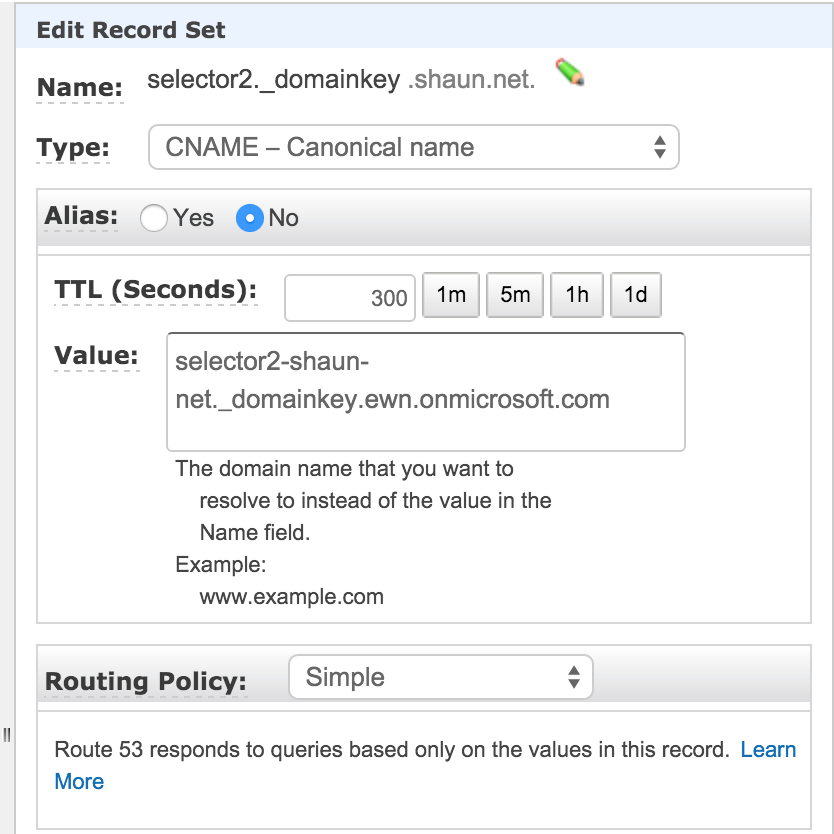
The records that I needed to create were:
selector1._domainkey.shaun.net. CNAME selector1-shaun-net._domainkey.ewn.onmicrosoft.com
selector2._domainkey.shaun.net. CNAME selector2-shaun-net._domainkey.ewn.onmicrosoft.com
The “shaun-net” is the domain GUID and can be retrieved from the MX record for your domain. Mine for example looks like:
shaun-net.mail.protection.outlook.com
I use AWS Route53 to host my DNS, so adding the records was as follows:
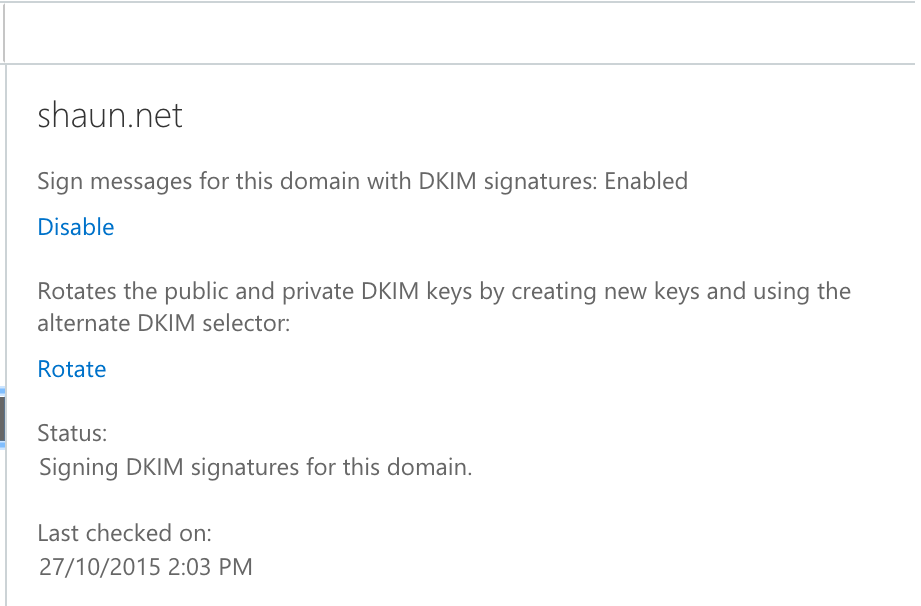
The second step was to enable DKIM signing on my domain. This isn’t yet available in the Office365 console but can be done using Powershell with Exchange Online.
The command I executed was:
New-DkimSigningConfig –DomainName shaun.net –Enabled $true
The output was as follows:
Domain Enabled
------ -------
shaun.net True
Once this was done I went to the Exchange Admin Center under Protection → DKIM. Here you can see that it has been enabled successfully.
With this in place I sent a message to my Gmail account and checked the headers for successful DKIM validation. Here it is!
Authentication-Results: mx.google.com;
spf=pass (google.com: domain of [email protected] designates 104.47.125.134 as permitted sender) [email protected];
dkim=pass [email protected]
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=shaun.example;
s=selector1; h=From:To:Date:Subject:Message-ID:Content-Type:MIME-Version;
bh=ukfgopG/NCPVHnV39aUVwCgP/uGi8cmejAx0fLDSQsQ=;
b=xqB/OODGfsE13tQN6xjrxrXHHjP6nTTqXWxnA2EZVFitABHh6MZ+zllm9YCkPi4bA5HS92nV8qmURi3YwEYnlRVXG4N6r7PPmPAZ1JZPMf985pmbp0uKjQcQqR0p/5hj2Essz9pgU9vGZlLx4jpU0ixn+KIfo2ISJEx9x6TABuE=
DKIM Outbound is still showing as rolling out on the Office 365 Roadmap so if this doesn’t work for you, your account may not have been activated to use this feature yet. Nonetheless it’s a very welcome feature and I’m pleased to see it was relatively easy to setup.